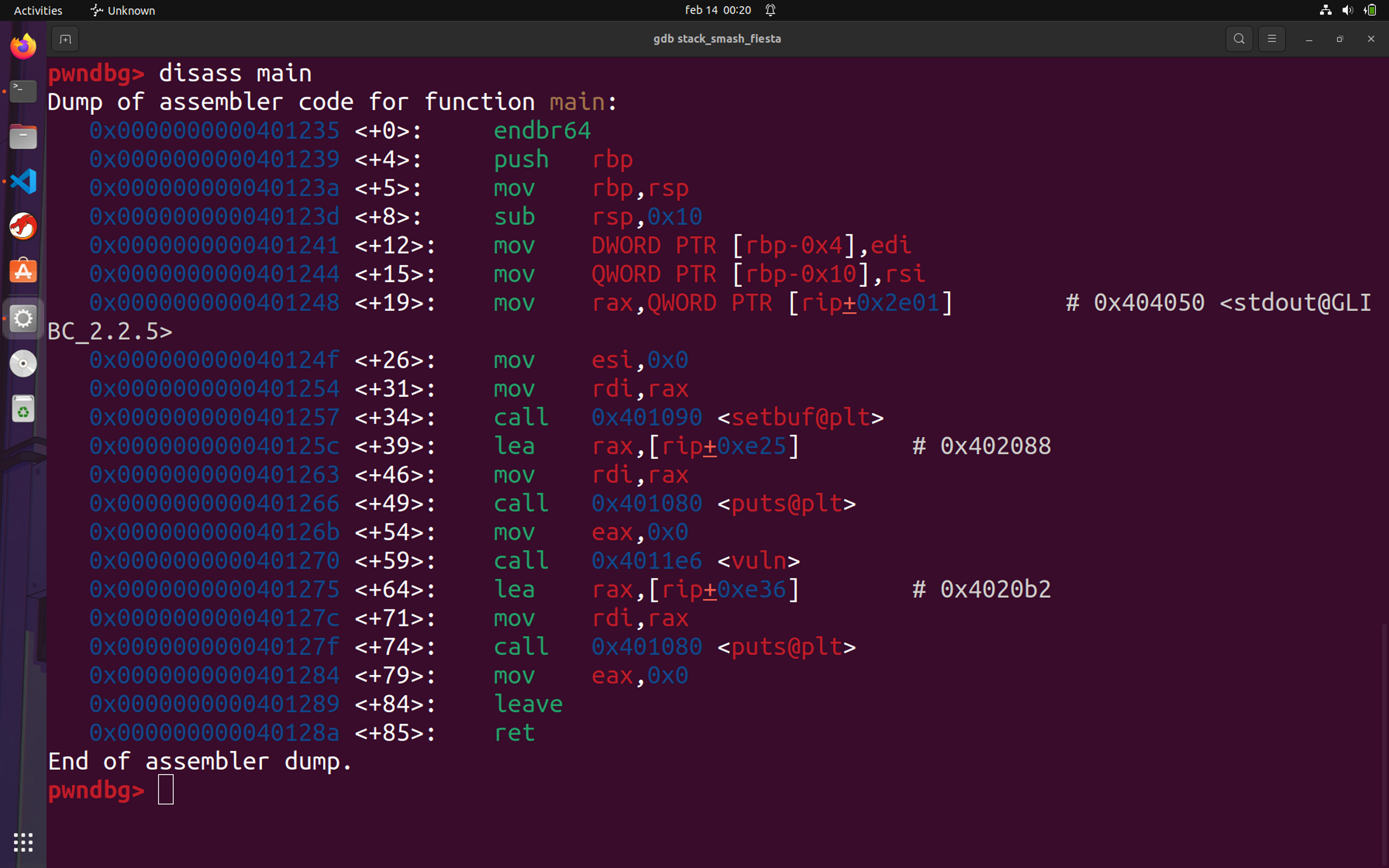
In this guide, we will walk through the complete process of creating a vulnerable C binary, compiling it with disabled security…
In this guide, we will walk through the complete process of creating a vulnerable C binary, compiling it with disabled security…Continue reading on Medium » Read More Hacking on Medium
#hacking