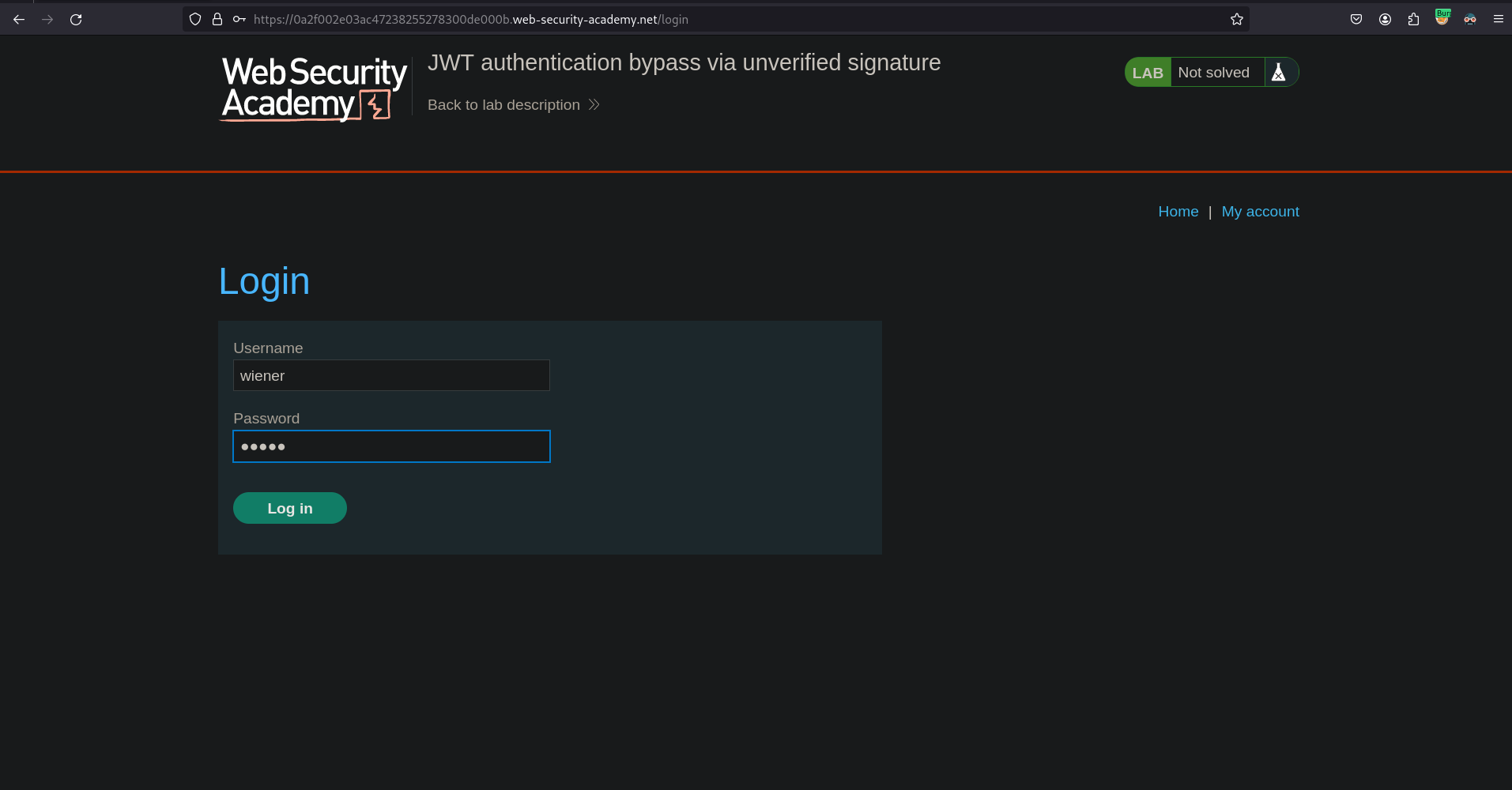
By design, servers don’t usually store any information about the JWTs that they issue. Instead, each token is an entirely self-contained…
By design, servers don’t usually store any information about the JWTs that they issue. Instead, each token is an entirely self-contained…Continue reading on Medium » Read More Hacking on Medium
#hacking