Manipulate a JWT authentication token to escalate privileges and learn why the “none” algorithm should rarely be used
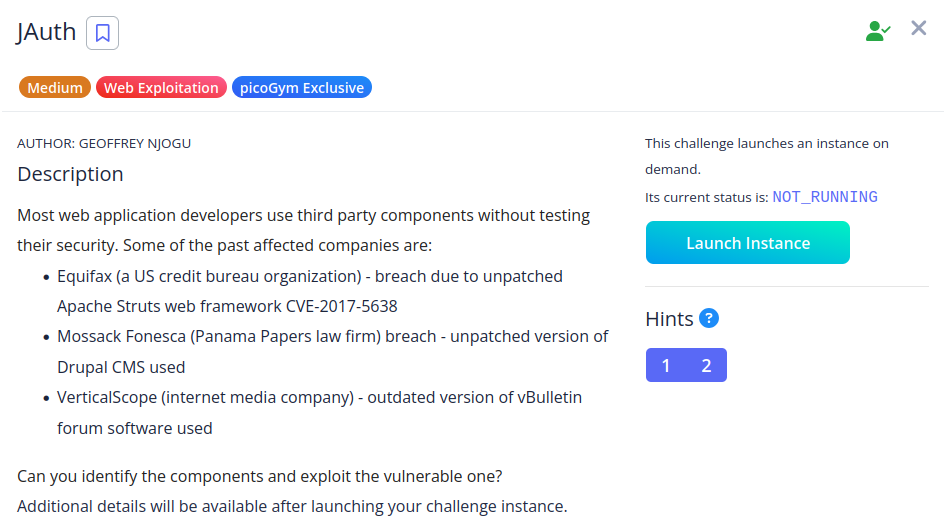 Manipulate a JWT authentication token to escalate privileges and learn why the “none” algorithm should rarely be usedContinue reading on Medium » Read More Hacking on Medium
Manipulate a JWT authentication token to escalate privileges and learn why the “none” algorithm should rarely be usedContinue reading on Medium » Read More Hacking on Medium
#hacking